Our Process
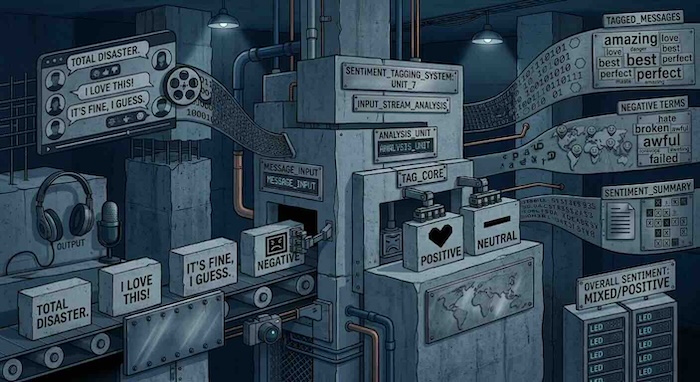
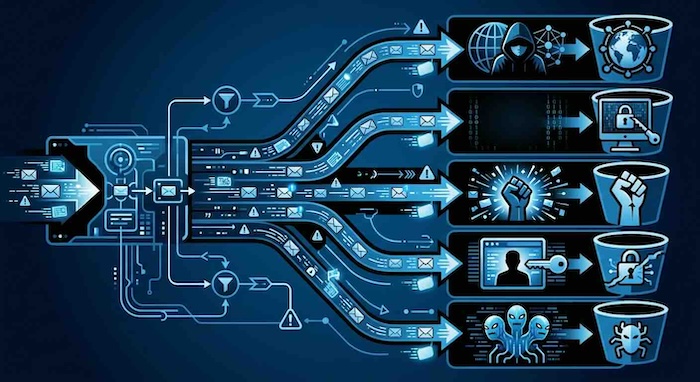
1) Collect OSINT
2) Enrich: Translate, Transcribe, Store Media, Classify, Tag
3) Connect Entities
4) Calculate Risk
User Risk Score
85/100
High Risk
- Known Criminal Associate
- Dark Web Activity
- Multiple Alias Use
Org Risk Score
60/100
Medium Risk
- Sanctioned Jurisdiction
- Shell Company Indicators
- Unusual Financial Flows
Crypto Risk Score
92/100
High Risk
- Stolen Funds Link
- Mixer Usage
- Ransomware Payment Association
5) Provide Autonomous Intelligence
Real-Time RFI Responses
AI
SUBJECT: OPERATION 'SILENT FLOW' - INTEL REPORT.
SUMMARY: Autonomous agents have identified a sophisticated money laundering operation involving cryptocurrency and shell companies.
KEY FINDINGS:
- The threat actor "Cyber_Ghost" has moved approximately .2M in BTC through mixer services. The funds were traced to a known darknet marketplace and consequently deposited into accounts associated with 'Apex Solutions'.
RECOMMENDATION:
Immediate freezing of assets in identified wallets and further investigation into 'Apex Solutions' corporate structure.
STATUS: REPORT GENERATING... [30%]
📄 Download Preliminary PDF
_
----------------------------------------
INCOMING RFI: FROM H.Q.
PRIORITY: HIGH
REQUEST: Confirm association between specific wallet 0x7a...4e9 and known Lazarus Group identifiers. Needed for OFAC designation packet.
STATUS: QUEUED FOR NEXT CYCLE
Ask Cloudburst
What is the connection between 'Cyber_Ghost' and 'Apex Solutions'?
Based on the analysis, Cyber_Ghost is listed as a director for 'Apex Solutions' under a loose alias. Furthermore, repeated transactions were detected from Cyber_Ghost's crypto wallets to Apex Solutions' corporate accounts.
Show me the direct logic chain.
1. 0x7a...4e9 (Cyber_Ghost wallet) ➔ Mixer_Alpha (Transaction ID: tx_992...)
2. Mixer_Alpha ➔ 0x3b...1c2 (Apex Solutions Holding)
3. DIRECT LINK confirmed via timing analysis (correlation 0.95).
2. Mixer_Alpha ➔ 0x3b...1c2 (Apex Solutions Holding)
3. DIRECT LINK confirmed via timing analysis (correlation 0.95).